Blog 1
DORA, Kesako ?
The Digital Operational Resilience Act (DORA) will become applicable on 17 January 2025. From that date all financial entities in its scope will need to have a comprehensive register of their contractual arrangements with ICT third-party service providers available at entity, sub-consolidated and consolidated levels.
This is a regulation from the European Bank Authority for all financial entities.
While all financial sector entities will be subject to DORA, ICT third-party providers who provide ICT services to financial entities and are identified as critical (critical third-party providers – CTPPs), will be subject to an EU oversight framework. The DORA oversight framework assigns to the three European Supervisory Authorities – ESAs (i.e. European Banking Authority – EBA , European Securities and Markets Authority – ESMA, European Insurance and Occupational Pension Authority – EIOPA) the role of Lead Overseer, to ensure that CTPPs are adequately monitored on a Pan-European scale, for the risks that they may pose to EU financial sector.
The registers will serve for:
- financial entities to monitor their ICT third-party risk,
- the EU competent authorities to supervise ICT and third-party risk management at the financial entities and
- the ESAs to designate the critical ICT third-party service provides (CTPP) which will be subject to an EU-level oversight.
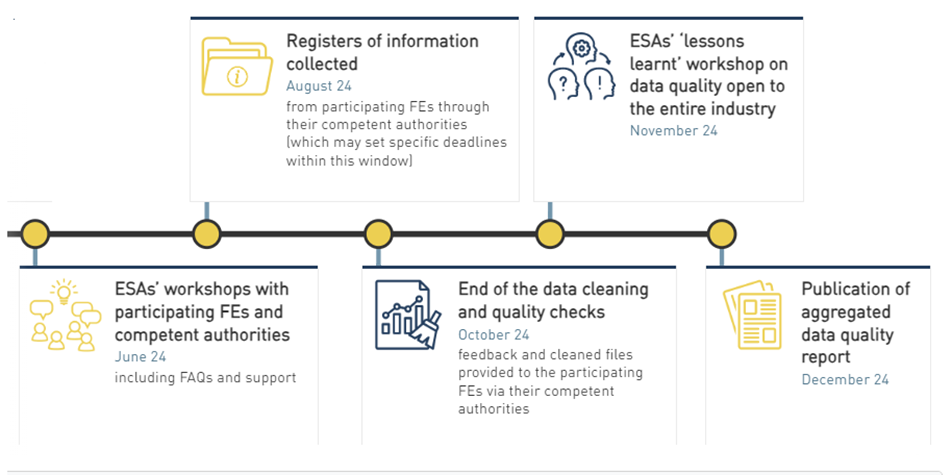
Timeline and milestones
Blog 2
The Top 5 of Cyber security Threats and how to defend against them. Source: ISACA
As the world becomes increasingly reliant on technology, the attack surface of cyberspace contiDefending against cyberthreats is a critical and ongoing process that requires a proactive and multifaceted approach. Social engineering, third-party exposure, cloud vulnerabilities, ransomware, and IoT are the top threats that organizations should focus on to protect their data, systems, and reputations. These threats can cause organizations to incur significant damage or loss if not addressed properly. As such, organizations should invest in security awareness programs, third-party management, cloud security, backup and recovery, and IoT security to help prevent and mitigate risk.
Additionally, collaborating with reputable security partners, staying informed about the latest threats and continuously reassessing and improving security practices are essential to effectively mitigate cyberrisk. By prioritizing cybersecurity and fostering a security-conscious culture, organizations can reduce the likelihood of successful cyberattacks and ensure more resilient and secure digital environments.
nues to expand. Cyberthreats have grown more sophisticated, posing significant risk to individuals, organizations and governments alike. It is imperative to examine the top cyberthreats faced by enterprises today and consider what preventive measures can be taken to safeguard digital assets and privacy.
Social Engineering
Unlike traditional hacking techniques, social engineering focuses on extracting information by exploiting psychology and reading the interaction patterns of humans. Cybercriminals manipulate human psychology to encourage the sharing of confidential information. This could include stealing login credentials or banking details, or unknowingly installing malicious software. These malicious cyberactors use social engineering as a tactic to bypass technological defenses. For example, an attacker could impersonate a bank representative on the phone to trick a victim into sharing personal information and use it to gain unauthorized access to their bank account.
Defending against social engineering requires a multilayered approach that involves a combination of technological solutions, robust policies and user awareness training. Several technological solutions that can help defend against social engineering are multifactor authentication (MFA), endpoint protection, email and web filtering, and intrusion detection and prevention systems (IDPS).
There should also be policies in place that address areas such as access control, data classification, data labelling and handling, incident response planning, social media use and password best practices.
Defending against social engineering requires a multilayered approach that involves a combination of technological solutions, robust policies and user awareness training.
In addition, employees should be trained in how to recognize phishing emails, suspicious phone calls or other avenues that are used by attackers to manipulate them. Staff should be informed about the latest threats and best practices for staying secure. A well-informed and security-conscious workforce is a critical component of any successful defense strategy.
Organizations can adopt several behaviors and attitudes to protect against social engineering mechanisms (figure 1).
Figure 1—Social Engineering: Rational, Wise, Emotional
By combining the following 3 strategies with a proactive and security-conscious approach, organizations can create a stronger defense against social engineering attacks and better protect their valuable assets and data:
- Rational measures
- Restrict access. Limiting access ensures that only authorized personnel can access sensitive information. This reduces the chances of attackers infiltrating the organization.
- Verify requests. Verifying requests, especially those involving financial transactions or access to sensitive data, helps confirm the legitimacy of the requestor.
- Offer education and training. Regularly educating and training employees on social engineering tactics and security best practices increases awareness and empowers them to recognize and resist manipulation attempts.
- Keep software updated. Regularly updating software and security patches minimizes vulnerabilities that attackers might exploit.
- Best practices
- Implement strong password policies. Enforcing strong password policies, such as requiring complex passwords and regular password changes, adds an extra layer of security against unauthorized access.
- Be cautious of unsolicited emails or calls. Encouraging vigilance when dealing with unsolicited emails or phone calls helps employees avoid falling for phishing schemes and other deceptive tactics.
- Emotional resilience
- React promptly. A swift response to security incidents minimizes damage and prevents further compromise. Organizations should have incident response plans in place.
- Encourage reporting. Creating a culture that encourages employees to report suspicious activities or potential security breaches ensures that threats are identified and addressed promptly.
- Promote a culture of security. When security is ingrained in an organization’s culture, employees are more likely to prioritize it in their daily activities.
- Engage leadership to gain support. Obtaining support from leadership provides necessary resources and sets an example for the entire organization, reinforcing the importance of security.
Combining these strategies means that organizations not only put preventive measures in place, but also create a responsive and resilient security environment. This comprehensive approach helps them stay ahead of evolving social engineering tactics, protect their valuable assets and data, and reduce the potential impact of security breaches. In essence, it transforms security from a mere set of rules and guidelines into a proactive and adaptive defense mechanism.
Third-Party Exposure
As organizations increasingly rely on third-party relationships for various aspects of their operations, the associated risk of utilizing third parties has become more pronounced and is critical to address. Every enterprise should be significantly concerned about the dangers of third-party risk today. However, there are effective ways to mitigate risk and safeguard organizational interests.
When any organization chooses to outsource its services or make use of software provided by a third party, they are not any less likely to experience risk themselves. Potential risk factors and vulnerabilities remain when an organization engages with external vendors, suppliers, contractors or partners. For example, consider a healthcare provider that outsources its medical billing services to a third party. Due to lax security practices at the third-party billing organization, patient medical records are compromised, leading to a data breach and potential legal and reputational repercussions for the healthcare provider.
Fortunately, there are several strategies an enterprise can employ to mitigate third-party risk (figure 2).
Figure 2—Key Strategies for Enhancing Third-Party Security
Defending against third-party exposure involves implementing a comprehensive risk management strategy to mitigate potential risk and protect an organization and its customers. By taking the following proactive measures, an organization can significantly reduce the risk of third-party exposure and establish a strong defense against potential security breaches originating from third-party vendors:
- Conduct thorough vendor assessments. Before entering any business relationship, conduct exhaustive security assessments and due diligence on all third-party vendors. An assessment typically involves scrutinizing a vendor’s security policies, practices and track record. This may also encompass reviewing its cybersecurity infrastructure, data protection measures and compliance with relevant industry regulations. By conducting this assessment, organizations can identify potential security risk associated with the vendor and make informed decisions about whether to engage with them. It helps prevent partnerships with vendors who may pose a security threat.
- Include security requirements in contracts. Ensure that security requirements are unequivocally outlined in contracts and service level agreements (SLAs) with third-party vendors. These requirements should outline the security measures expected from the vendor, such as encryption protocols, access controls, regular security audits, and compliance with specific security standards or regulations. Having security requirements in contracts helps establish a legal framework for holding the vendor accountable for maintaining a certain level of security. It provides recourse in case of breaches and serves as a deterrent against negligence. These SLAs should specify who is responsible for what aspects of security, how data breaches will be addressed, and the consequences or compensation in the event of a security incident.
- Create incident response plans. Develop and consistently update incident response plans that delineate how the organization and third-party vendors will respond to security incidents. Incident response plans outline the steps to take when a security incident occurs. They include procedures for identifying, containing, mitigating and recovering from breaches. These plans should involve both the organization and the third-party vendor. Incident response plans ensure a coordinated and organized response to security incidents, minimizing damage and downtime. They also promote transparency and collaboration between the organization and its vendors, facilitating a unified approach to security.
Cloud Vulnerabilities
Cloud service providers (CSPs) invest heavily in security infrastructure by offering encryption, distributed denial-of-service (DDoS) protection, identity management services, compliance certifications, vulnerability scanning and incident response tools, and more. CSPs also use automation and machine learning (ML) to detect threats and provide customers with tools and resources to maintain secure cloud environments, making cloud platforms generally more secure than traditional on-premises systems for many organizations. However, it is essential to recognize that no system is entirely immune to risk.
Cloud vulnerabilities refer to security weaknesses and risk factors associated with cloud computing environments. While cloud services offer numerous benefits, they also present unique security challenges including potential data breaches, insecure application programming interfaces (APIs) or data storage, account hijacking and more. For example, failure to apply timely security updates and patches to cloud-based applications and infrastructure exposes vulnerabilities that attackers can exploit to gain unauthorized access or compromise data. Fortunately, there are several essential strategies available to build an effective cloud security defense (figure 3).
Figure 3—Cloud Defense Strategies
There are 6 recommended strategies for defending against cloud vulnerabilities:
- Conduct a thorough cloud provider assessment. Before entrusting a cloud provider with data and applications, a thorough assessment of their security practices, infrastructure, and track record is essential. This ensures that the cloud partner meets security standards and reduces the risk of vulnerabilities.
- Utilize identity and access management systems. IAM systems enable organizations to control and manage user access to cloud resources, ensuring that only authorized individuals can access critical data and services. IAM also allows the enforcement of security policies, including MFA.
- Deliver security patches regularly. Cloud providers regularly release security updates and patches to address known vulnerabilities. Applying these patches promptly is crucial to close security gaps and prevent exploitation.
- Create data backups and disaster recovery plans. Data loss or system downtime can result from various factors including cyberattacks, hardware failures or natural disasters. Implementing robust data backup and disaster recovery plans ensures data resilience and business continuity.
- Bolster network security. Securing the network infrastructure within a cloud environment is crucial to protect data in transit and ensure the isolation of resources. This includes implementing firewalls, intrusion detection systems and encryption.
- Prioritize compliance and audit. Compliance with industry regulations and standards is essential for data protection, risk mitigation and maintaining trust with customers. Regular audits ensure adherence to these standards and help identify areas for improvement.
Defending against cloud vulnerabilities is critical to protecting sensitive data, ensuring compliance with regulations, maintaining business continuity and upholding trust with customers and partners. By prioritizing cloud security, organizations can reduce the risk of cyber incidents and preserve their reputation in an increasingly digital and interconnected world.
Ransomware
Ransomware is a type of malicious software (i.e., malware) designed to encrypt or block access to a victim’s files or computer system until a ransom is paid to the attacker. In recent years, ransomware has become one of the most reoccurring forms of cyberattack. The average ransom demand in 2021 was US$5.3 million.1
Ransomware attacks can cause significant disruption to individuals and organizations. They can lead to data loss, financial losses due to downtime and ransom payments, reputational damage and legal and regulatory consequences. For example, an ecommerce retailer that is targeted by a cyberattack may lose the ability to process orders and could suffer substantial financial losses. The enterprise may be forced to pay a ransom to regain access to their data. Meanwhile, while systems are down, a a loss of revenue often occurs due to business interruption.
Thus, prevention is crucial. Recovering from a ransomware attack can be challenging and costly, but with the right tactics (figure 4), it is possible.
Figure 4—Defending Against Ransomware Attacks
There are 7 strategies that can be used to defend against ransomware attacks:
- Save data backups regularly. Habitually backing up data is one of the most effective defenses against ransomware. If data is compromised or encrypted by ransomware, having up-to-date backups ensures that critical information can be recovered without paying a ransom.
- Implement effective endpoint protection measures. Ransomware often targets individual endpoints, such as computers and mobile devices. Strong endpoint protection solutions, including antivirus software and advanced threat detection, can help prevent ransomware from gaining a foothold.
- Enable firewalls. Firewalls act as barriers between a network and potential threats it may face, including ransomware. Configuring and enabling firewalls can help block malicious traffic and prevent ransomware from infiltrating systems.
- Utilize network segmentation. Segmenting a network into isolated zones limits the lateral movement of ransomware within an organization. Even if ransomware infects one part of the network, with network segmentation, it is less likely to spread to other segments.
- Employ email and web filters. Many ransomware attacks begin with phishing emails or via malicious websites. Email and web filtering solutions can block suspicious emails and web content, reducing the risk of users inadvertently downloading ransomware.
- Stay informed. Ransomware threats are continually evolving. Staying informed about the latest ransomware strains, tactics and vulnerabilities is crucial for proactive defense.
- Conduct regular security audits. Conducting regular security audits helps identify vulnerabilities and weaknesses in an organization’s security posture. It enables practitioners to address issues before they can be exploited by ransomware.
By implementing these 7 measures and maintaining a security-conscious culture, one can significantly reduce the risk of falling victim to ransomware and strengthen an organization’s resilience against cyberthreats.
Attacks on IoT Devices
The Internet of Things (IoT) refers to the interconnection of everyday physical devices and objects with the Internet, enabling them to collect and exchange data. These connected devices, often equipped with sensors and processors, can communicate with each other and with central systems without requiring human intervention.
IoT devices are vulnerable to cybercrime due to weak security measures, a proliferation of devices increasing the attack surface, the formation of botnets for large-scale attacks, a lack of updates and potential ransomware attacks, among other factors.
Collaboration among stakeholders, adherence to security best practices and ongoing awareness of ever-changing threats can help mitigate the risk associated with cybercrime in the IoT ecosystem (figure 5).
Figure 5—Strategies for Safer IoT Devices
There are 5 effective strategies for safeguarding organizations IoT devices in today’s digital and interconnected landscape:
- Adhere to rigorous authentication protocols. Ensuring that only authorized users and devices can access connected devices is fundamental for security. Strong authentication mechanisms, such as passwords, biometrics, or MFA, help prevent unauthorized access.
- Update firmware and software in a timely manner. Regular updates and patches are essential for addressing known vulnerabilities in connected devices. Outdated firmware and software can become easy targets for attackers.
- Conduct IoT security testing. Conduct penetration testing, perform vulnerability scanning and take security assessments to assess device security. Address identified issues promptly and iteratively test security.
- Dispose of devices securely. When disposing of or decommissioning connected devices, data must be securely wiped to prevent unauthorized access to sensitive information.
- Adhere to regulatory compliance mandates. Compliance with relevant regulations and standards ensures that connected devices meet security and privacy requirements. Noncompliance can result in legal and financial consequences.
By adopting these proactive measures, organizations can strengthen their IoT security postures and minimize the risk associated with connected devices. This allows organizations to safeguard sensitive data and maintain the integrity of their networks.
Conclusion
Defending against cyberthreats is a critical and ongoing process that requires a proactive and multifaceted approach. Social engineering, third-party exposure, cloud vulnerabilities, ransomware, and IoT are the top threats that organizations should focus on to protect their data, systems, and reputations. These threats can cause organizations to incur significant damage or loss if not addressed properly. As such, organizations should invest in security awareness programs, third-party management, cloud security, backup and recovery, and IoT security to help prevent and mitigate risk.
Additionally, collaborating with reputable security partners, staying informed about the latest threats and continuously reassessing and improving security practices are essential to effectively mitigate cyberrisk. By prioritizing cybersecurity and fostering a security-conscious culture, organizations can reduce the likelihood of successful cyberattacks and ensure more resilient and secure digital environments
Source: ISACA
Blog 3
Intelligence Artificielle : tout le monde en parle. Qu’en pensez-vous ?
IA ou Intelligence Atificielle, tout le monde en parle, de quoi s’agit-il exactement ? Selon Wikipedia, il s’agit d’un ensemble de théories et de techniques visant à réaliser des machines capables de simuler l’intelligence humaine, qui elle-même est caractérisée par plusieurs aptitudes, surtout cognitives, qui permettent à la machine d’apprendre, de former des concepts, de comprendre, d’appliquer la logique et la raison.
Le concept consiste donc à simuler ces aptitudes cognitives humaines, pour que les machines appliquent une certaine logique. Par aptitudes cognitives, on entend un processus qui se rapporte à la fonction de connaissance, et mettent en jeu la mémoire, le langage, le raisonnement, l’intelligence, la résolution de problèmes, la prise de décision, la perception ou l’attention. C’est pourquoi, toute IA a besoin de données importantes pour apprendre, pour les stocker de façon logique, afin d’en tirer des conclusions ou résultats.
Le plus connu des IA est bien ChatGPT (Generative Pre-trained Transformer) qui est un prototype d’agent conversationnel utilisant l’intelligence artificielle, développé par OpenAI et spécialisé dans le dialogue. (ChatGPT (openai.com)
Aujourd’hui, Microsoft a aussi renforcé son propre moteur de recherche par Bing, un assistant alimenté par l’IA.
Quel est donc l’avantage de ChatGPT dans notre quotidien ?
Pour les particuliers, cet outil va révolutionner la recherche d’information sur Internet, encore faut-il savoir le manipuler avec précaution.
En effet, comme il fait appel aux informations stockées sur le Web, et les restitue, en imitant le langage humain, ChatGPT nous donne un résultat assez épatant, avec une certaine précision, grâce à sa fonction d’auto-apprentissage. Le résultat en question, dépendra donc des informations véhiculées sur Internet. Et c’est bien là qu’il faudra être vigilant, car les données sur le Web, on le sait, doivent être manipulées avec parcimonie, du fait des sources différentes. Et c’est bien le souci avec ChatGPT, ce dernier ne révèle pas ses sources.
Pour les entreprises, cet outil a déjà révolutionné certains métiers, et d’autres sont en train de se métamorphoser. Selon l’institut Sapiens, cinq groupes d’emplois seront menacés par l’IA. Il s’agit surtout des emplois dont les tâches sont automatisables.
« Ce sont près de 2,1 millions d’actifs concentrés dans ces cinq métiers qui ont une forte probabilité de voir leur emploi disparaître dans les prochaines années », est-il écrit dans l’étude publiée mardi 21 août 2018 : « L’Impact de la révolution digitale sur l’emploi »
Employés de banque et assurance. En effet, l’effet numérique a conduit la fermeture d’agences au profit des opérations sur Internet .
- Employés de la comptabilité : la tendance est à l’externalisation du métier. Le rapport prévoit une extinction entre 2041 et 2056, quand « des logiciels intelligents dédiés pourront ainsi effectuer les tâches comptables sans intervention humaine »
- Secrétaire de bureautique et de direction. Ces postes ont déjà commencé à diminuer depuis l’an 2000 avec l’arrivée de l’informatique. Leur extinction est prévue entre 2053 et 2072 avec l’IA.
- Caissiers et employés de libre-service : « Les caisses automatiques permettent de diminuer drastiquement la masse salariale fleurissent depuis plusieurs années dans les supermarchés ».remarquent les auteurs de l’étude, qui projettent une extinction du métier à 2050 ou 2066.
- Ouvriers de la manutention : la disparition de ce métier est estimée au plus tôt en 2071 et au plus tard en… 2091
Pour conclure, l’IA a déjà révolutionné notre quotidien, et ce n’est que le début. L’accès à l’information sera encore plus facilité, mais au prix de l’intégrité et la véracité de l’information.
Nous attirons ici, votre attention, sur deux points qui nous semblent essentielles : il faudra toujours vérifier l’intégrité de l’information, ne pas faire confiance aveuglément aux résultats fournis par ces outils. Il conviendra de les vérifier au travers d’autres sources.
Nous vous conseillons également de diversifier les moteurs de recherche, afin de pouvoir croiser les informations recueillies par ces IA.
En somme, ces outils sont très pratiques, mais il ne s’agit que d’une aide à la décision. Il nous appartient de réfléchir, et d’analyser leurs résultats, pour les utiliser à bon escient.
Blog 4
Qu’est-ce que la Cybersécurité ?
Avec la montée de la dématérialisation, et le nombre de données échangées sur la toile, le risque Cyber a plus que doublé ces dernières années. Il est donc fondamental de se protéger afin de garantir la sécurité de notre actif le plus précieux : nos données.
La cybersécurité consiste à l’ensemble de dispositifs mis en place par une organisation ou un particulier à protéger ses données : sa confidentialité, son intégrité, sa disponibilité et sa traçabilité (CIAT).
Pour cela, il est important d’évaluer le risque Cyber afin d’identifier les mesures adéquates à mettre en place. Ce principe s’appelle la gestion des risques cyber, qui s’inscrit dans le cadre de la gestion des risques, en général.
Pour une entreprise, la gestion du risque cyber est composée de 4 grandes étapes :
- Identification du risque
- Analyse du risque
- Evaluation
- Priorisation des différents risques et menaces qui pourraient affecter le patrimoine de l’entreprise.
Selon Cisco, les menaces Cyber peuvent être classées en 4 grandes familles :
- Le « Phishing » ou hameçonnage qui consiste à attirer l’utilisateur à cliquer sur un lien malveillant. Dans un email ou bien un SMS, le fraudeur se fait passer pour un organisme qui vous est familier (banque, administration fiscale, caisse de sécurité sociale…), en utilisant son logo et son nom. Vous recevez un courriel dans lequel il vous est demandé de “mettre à jour” ou de “confirmer suite à un incident technique” vos données, notamment bancaires
- Le « Social Engineering » ou attaques informationnelles pour exploiter les réseaux sociaux avec une attaque informatique pour nuire à l’image
- Le « Ransomware » ou rançongiciel qui est un logiciel téléchargé par inadvertance sur votre ordinateur et qui vous bloque son accès jusqu’à ce qu’un rançon soit payé.
- Le « Malware » qui est un virus qui se greffe à un autre programme, et qui lorsqu’il est exécuté (généralement sans que l’utilisateur le sache) se répète en modifiant d’autres programmes informatiques et en les infectant avec ses propres morceaux de code.
Ainsi, comme on peut le constater, la cible de l’attaquant reste l’être humain par lequel l’attaquant exploite ces vulnérabilités. Il donc important d’adopter les bonnes pratiques suivantes préconisées par l’ANSII :
- renforcer l’authentification sur les systèmes d’information ;
- accroître la supervision de sécurité ;
- sauvegarder hors-ligne les données et les applications critiques ;
- établir une liste priorisée des services numériques critiques de l’entité ;
- s’assurer de l’existence d’un dispositif de gestion de crise adapté à une cyberattaque.
Ces mesures prioritaires de cybersécurité sont essentielles et leur mise en œuvre à court terme permet de limiter la probabilité d’une cyberattaque ainsi que ses potentiels effets. Pour être pleinement efficaces, elles doivent cependant s’inscrire dans une démarche de cybersécurité globale et de long terme.
